This year cyberattacks have yet again, reached record numbers. 2019 has seen a new threat emerge that has even caught the attention of the Department of Homeland Security and the FBI Cyber Unit. IT service providers have been the target of new ransomware attacks. Yes, the very people that are entrusted to secure and support your network infrastructure found themselves locked out of their client’s systems (and their own). This caused massive downtime, data loss and the financial impact is yet to be disclosed but the initial estimates are record-breaking.
So, who was hit and why? Let’s start by breaking down the list. IT service providers that were targeted include the following:
- MSSP – Managed Security Service Provider
- MSP – Managed Service Provider
- CSP – Communications Service provider
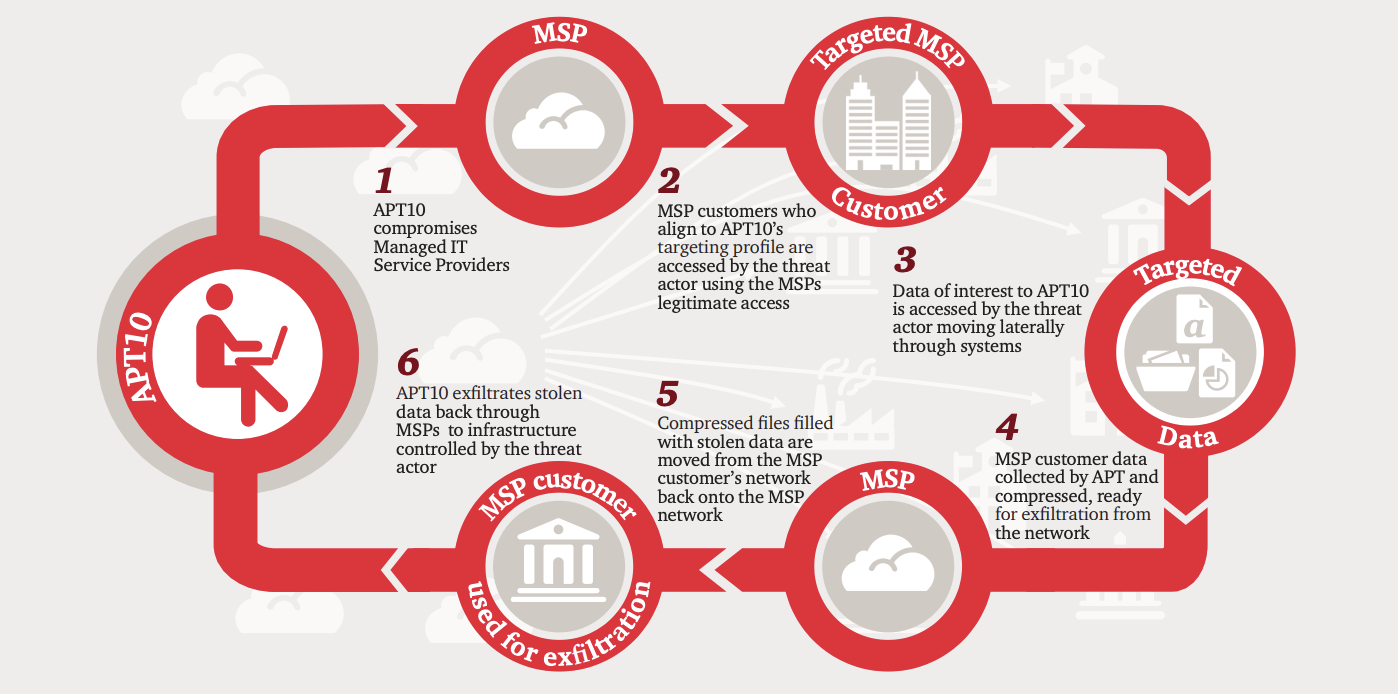
Why were these specific IT service providers targeted? Three simple letters, R, M, M or Remote Monitoring Management. Remote monitoring and management (RMM), also known as network management or remote monitoring software, is a type of software designed to help managed IT service providers (MSPs) remotely and proactively monitor client endpoints, networks and computers. This is also now known as or referred to as remote IT management.
Now you know The Who, let’s go over The Why. Those targeted all use one type or another of RMM software. This is how they all remote access, monitor and support their clients/customers. Without the use of a robust RMM solution, networks worldwide would soon come to a grinding and abrupt halt. Not maybe. Not probably and not eventually. This is a fact and this is now a very popular vulnerability that has been discovered and is being exploited this very second. Let me break it down for you. Let’s just say for the sake of argument, you wanted to go out and steal 300 cars tonight. If you’ve seen the movie, “Gone in 60 Seconds” you’ll probably recall the many obstacles that had to be overcome to steal 48 cars in one night. Remember now? Ok, now what if Nicolas Cage and Angelina Jolie could have just pulled into their local Automall, strutted inside and opened a lockbox with the keys to all 48 cars (for this example it’s 300). See how easy that would be? Nearly effortless once that lockbox was opened and in case I lost you in translation, that RMM used by IT providers to perform their job and access their clients’ systems, IS THE LOCKBOX.
Is Your IT Provider Doing What’s Necessary?
IT Providers are considered high targets and we take this threat very seriously. If we are breached our clients will be the ones victimized. Our efforts include but are not limited to the following:
- 24/7 Threat Monitoring
- Realtime Ransomware Protection – Heuristic & Suspicious Characteristics Examination and Termination
- Compliance Auditing
- Layered Security Stacking
- Aggressive Patching Methodology
- Penetration & Vulnerability Testing
- Antivirus, AntiSpam Protection
- Web Filtering
- Social Engineering Training
- Phishing Techniques Education and Training
When you put your business’s cybersecurity on the line you’d best trust your MSP’s reputation and track record. How seriously do they take security? Do they put on a good show or are they able to answer your questions immediately and completely? What steps are they taking to address current and emerging threats? If ransomware were to penetrate your network, what would be their steps to ensure full recovery and how long do they anticipate the process will take?
Also, it’s common to ask what RMM your MSP is using. IT Departments have no problem asking other IT Departments what’s in their applications arsenal. We want to know and for good reason. It doesn’t take long to research many of the more popular and commonly found RMM solutions. See how they compare and stack up against the competition. Is your MSP using an exploited RMM solution? Is your network security a ticking timebomb?